The $293 million bug wasn't in the code; so, what's the deal with the "DVN Configuration Bug," which led to the largest hack of 2026?
On April 18, 2026, the liquidity restaking protocol of Kelp DAO was exploited, with the attacker siphoning off 116,500 rsETH from a cross-chain bridge within hours, amounting to approximately $293 million at the time. The entire process was efficiently executed with a hint of anomaly, starting from a forged cross-chain message to laundering the stolen funds across Aave V3, Compound V3, and Euler lending protocols with real assets borrowed. The attacker swiftly exited with $236 million worth of WETH on the same day. Aave, SparkLend, and Fluid promptly froze the rsETH market.
This marks the largest DeFi exploit event of 2026.
However, one aspect distinguishes this attack from most hacking incidents. The smart contract code of Kelp DAO had no vulnerabilities. Security researcher @0xQuit, involved in the investigation, stated on X, "From what I currently understand, this is a combination of two issues: a 1-of-1 DVN configuration and the compromise of the DVN node itself." In their official statement, LayerZero did not blame the contract code, categorizing the issue as an "rsETH vulnerability" rather than a "LayerZero vulnerability."
$293 million was not in any line of code. It was concealed within a misconfigured parameter during deployment.
The common logic behind DeFi security audits is: find the contract, read the code, find vulnerabilities. This logic operates quite smoothly when dealing with code logic vulnerabilities. Tools like Slither and Mythril are mature in detecting known patterns such as reentrancy attacks and integer overflows. The widely promoted LLM for assisting in code audits also has some capability in identifying business logic vulnerabilities (e.g., flash loan arbitrage paths).
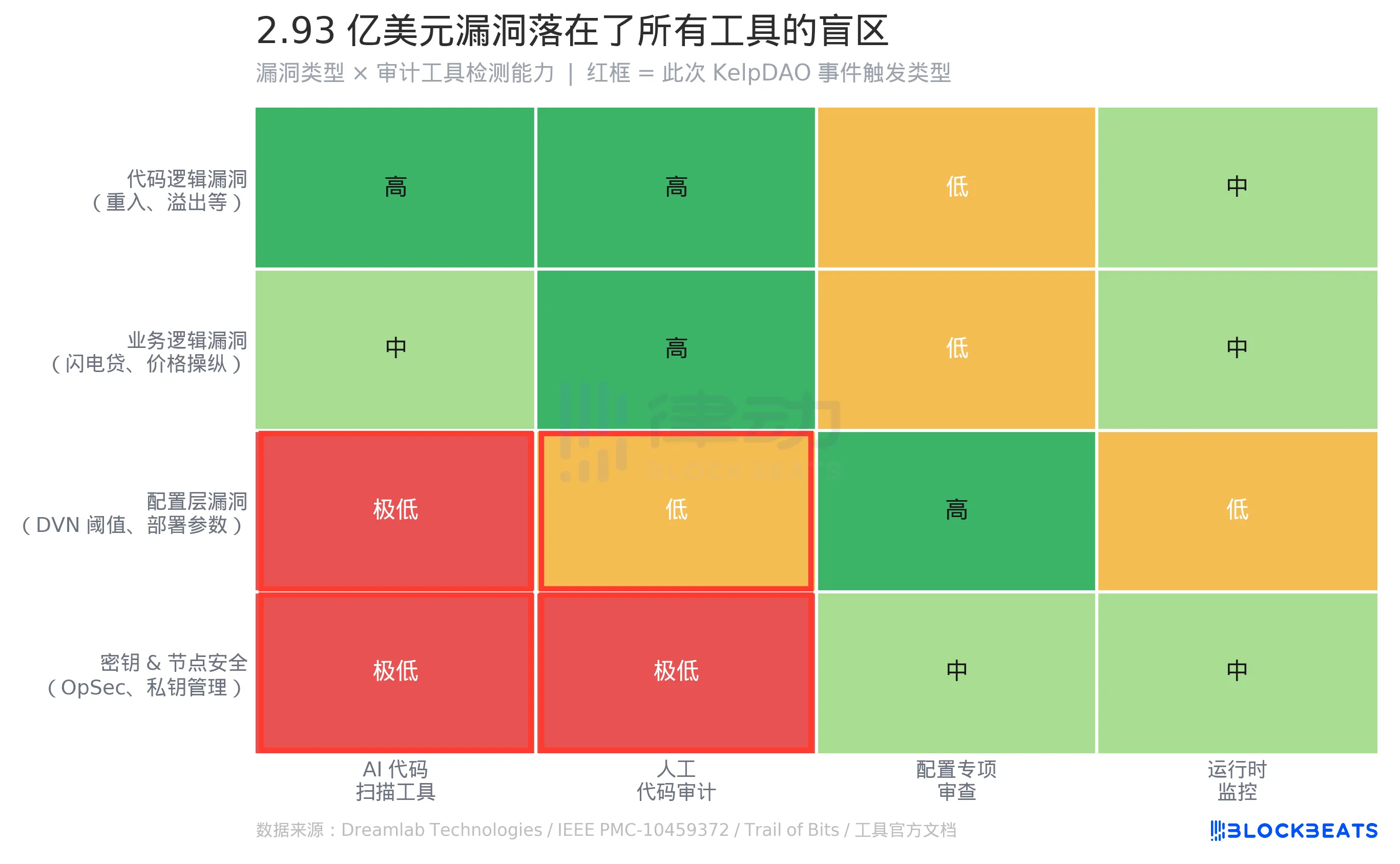
However, in this matrix, two rows are marked in red.
Configuration-level vulnerabilities fall into a structural blind spot in tool-based audits. The issue with Kelp DAO was not in a .sol file but in a parameter—DVN threshold—written during protocol deployment. This parameter determines how many validating nodes a cross-chain message must pass through to be considered valid. It's not in the code, not within Slither's scanning scope, nor in Mythril's symbolic execution path. According to Dreamlab Technologies' comparative study, Slither and Mythril detected 5/10 and 6/10 vulnerabilities in the tested contract, respectively. However, these results are based on the premise that the vulnerabilities exist in the code. According to IEEE research, even at the code level, existing tools can only detect 8%-20% of exploitable vulnerabilities.
From the perspective of the current audit paradigm, there is no tool that can "detect whether the DVN threshold is reasonable." To detect this type of configuration risk, what is needed is not a code analyzer, but a specialized configuration checklist: "Is the number of DVNs for the cross-chain protocol ≥ N?" "Is there a minimum threshold requirement?" Such questions are currently not covered by standardized tools and there is no widely recognized industry standard.
Also within the red zone is key and node security. In @0xQuit's description, it is mentioned that a DVN node was "compromised," which falls under Operational Security (OpSec) and is beyond the detection boundary of any static analysis tool. Whether it is a top-tier auditing firm or an AI scanning tool, none have the ability to predict whether a node operator's private key will be leaked.
This attack simultaneously triggered two red zones in the matrix.
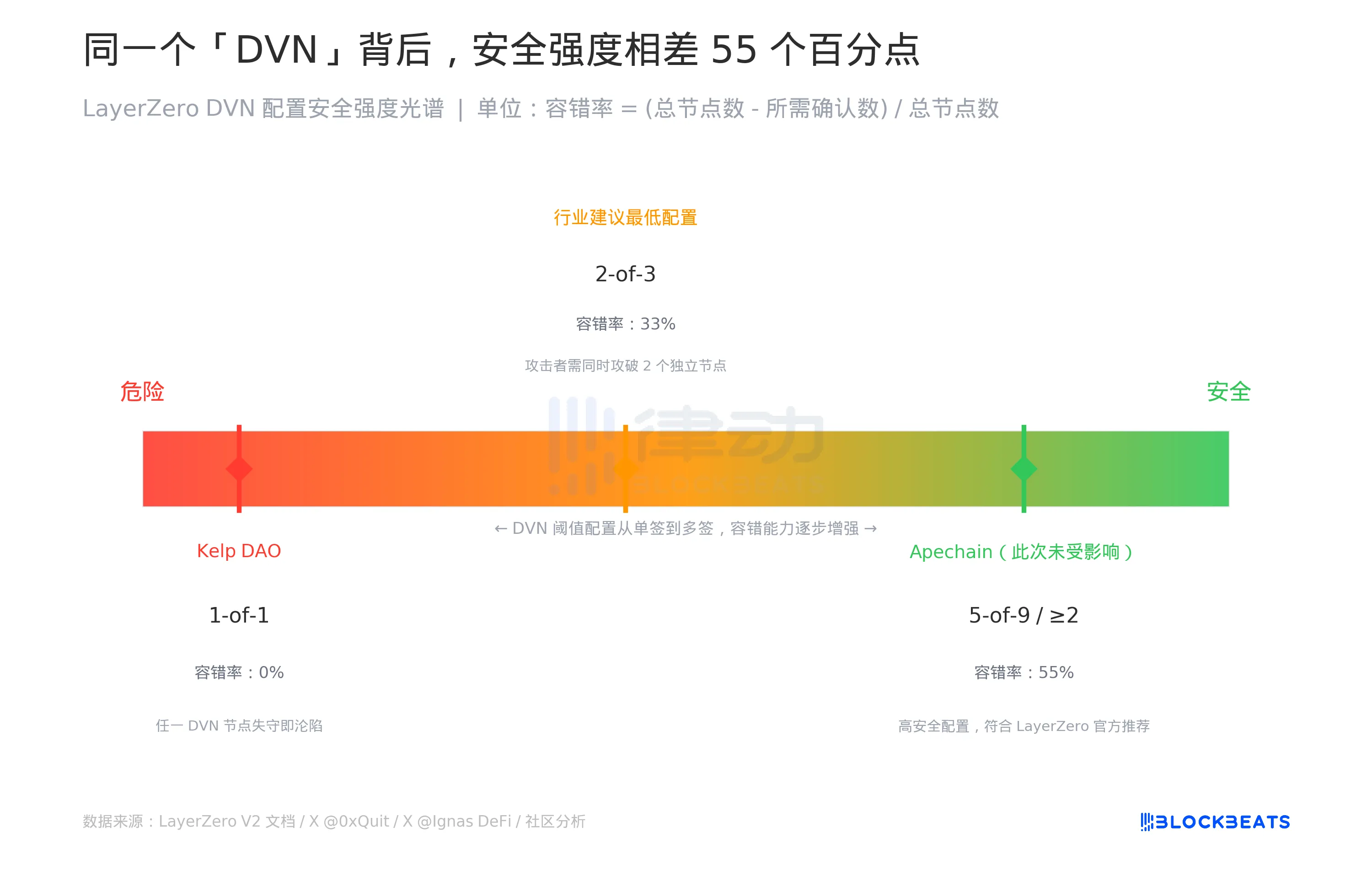
DVN is the cross-chain message verification mechanism of LayerZero V2, fully named Decentralized Verifier Network. Its design philosophy is to entrust security decision-making to the application layer: each protocol connecting to LayerZero can choose the number of DVN nodes required to confirm before allowing a cross-chain message to pass.
This "flexibility" has created a spectrum.
Kelp DAO chose the far-left end of the spectrum with a 1-of-1, requiring only one DVN node to confirm. This means a fault tolerance of zero, as an attacker only needs to compromise that single node to forge any cross-chain message. In contrast, Apechain, also connected to LayerZero, configured more than two required DVNs and was not affected by this event. The wording in the LayerZero official statement was, "All other applications remain secure," implying that security depends on the selected configuration.
The standard industry recommendation is at least 2-of-3, where an attacker would need to compromise two independent DVN nodes simultaneously to forge a message, increasing fault tolerance to 33%. A high-security configuration like 5-of-9 can raise fault tolerance to 55%.
The issue is that external observers and users cannot see this configuration. Also known as being "supported by LayerZero," the backend could range from 0% fault tolerance to 55% fault tolerance, both referred to as DVN in the documentation.
Seasoned crypto investor Dovey Wan, who experienced the Anyswap incident, directly stated on platform X: "LayerZero's DVN turned out to be a 1/1 validator... All cross-chain bridges should immediately undergo a comprehensive security review."
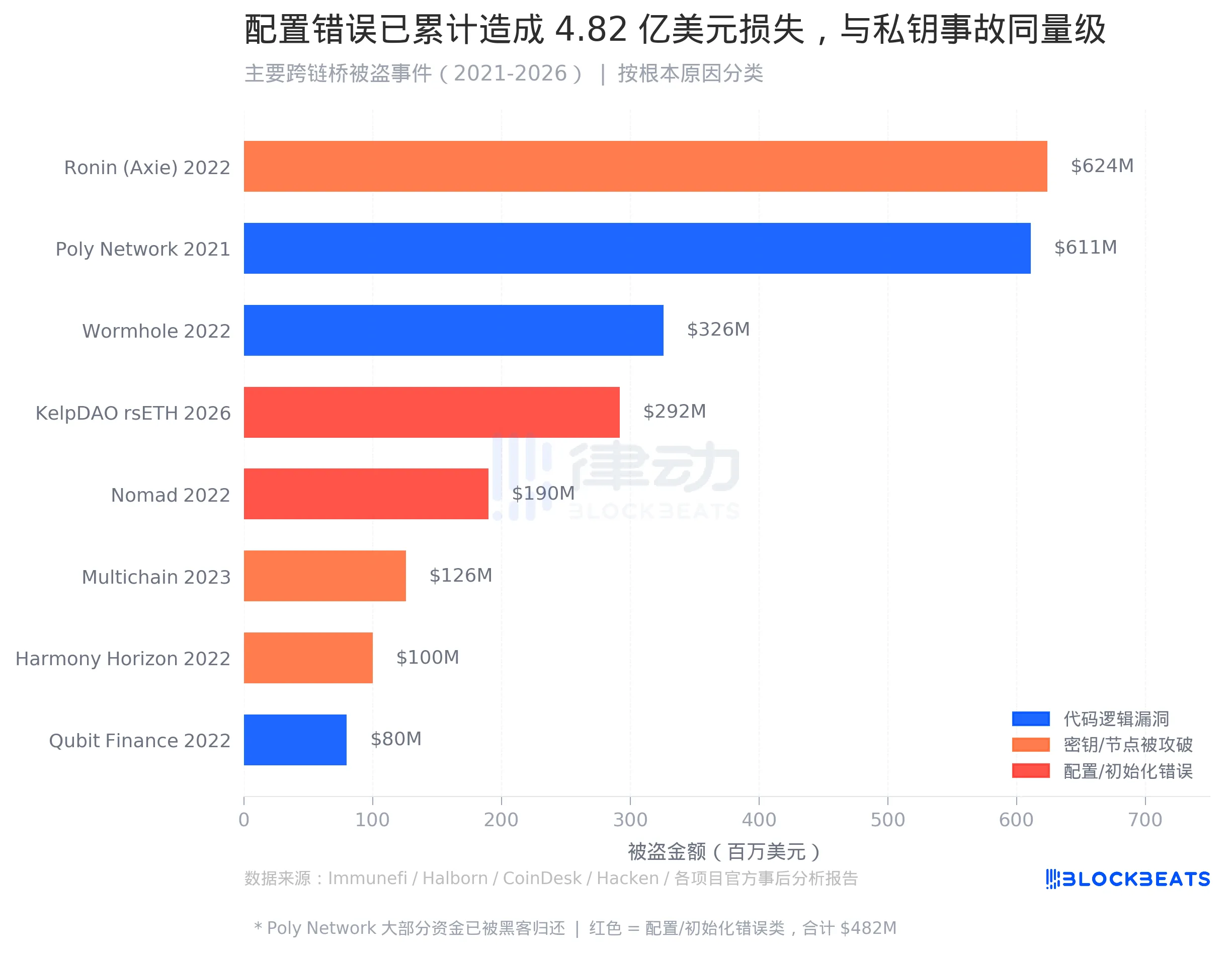
In August 2022, a vulnerability was discovered in the Nomad cross-chain bridge. Someone replicated the initial attack transaction, made minor modifications, and found success, leading to hundreds of addresses replicating the exploit and draining $190 million in a matter of hours.
Postmortem analysis by Nomad attributed the vulnerability to "initializing the trusted root as 0x00 during a routine upgrade." This was a configuration error that occurred during the deployment phase. The Merkle proof validation logic and the code itself were sound; the issue stemmed from an incorrect initial value.
Combining this incident with previous ones involving Nomad, configuration/initialization vulnerabilities have now resulted in approximately $482 million in losses. In the history of cross-chain bridge exploits, this category's scale now rivals that of key exposure incidents (e.g., Ronin $624 million, Harmony $100 million, Multichain $126 million, totaling around $850 million).
However, the product design of the code auditing industry has never been focused on this category of vulnerabilities.
Most discussions in the industry still revolve around code logic bugs. Incidents like Wormhole's $326 million exploit due to signature verification bypass and Qubit Finance's $80 million loss due to a fake deposit event are well-analyzed with detailed vulnerability reports, CVE references, and reproducible PoCs, making them suitable for audit tool training and optimization. Configuration layer issues are not explicitly coded, making it challenging to address within the production cycle.
One notable detail is the distinct triggering mechanisms of the two configuration-related events. Nomad's error stemmed from inadvertently setting an incorrect initial value during a routine upgrade, constituting a mistake. On the other hand, Kelp DAO's 1-of-1 incident was an active configuration choice—LayerZero protocol did not prohibit this option, and Kelp DAO did not violate any protocol rules. A "compliant" configuration choice and a "mistaken" initial value both led to the same outcome in the end.
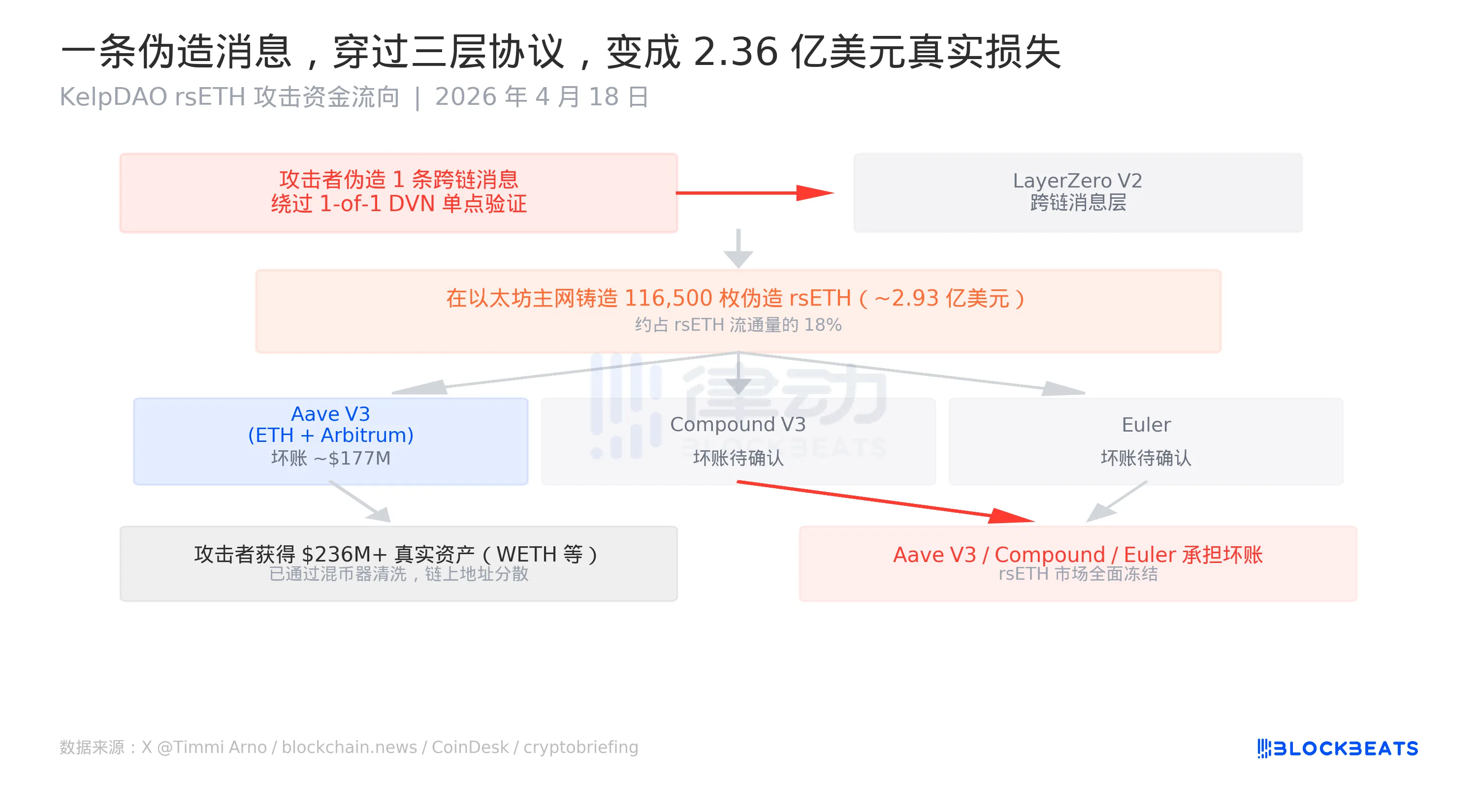
The execution logic of this attack was straightforward. A forged cross-chain message informed the Ethereum mainnet that "someone had already locked up an equivalent asset on another chain," triggering the minting of rsETH on the mainnet. The minted rsETH itself had no real backing, but its on-chain record was "valid" and could be accepted by lending protocols as collateral.
The attacker then dispersed 116,500 rsETH to Aave V3 (Ethereum and Arbitrum), Compound V3, and Euler, borrowing over a total of $236 million in real assets. According to multiple sources, the standalone default estimate for Aave V3 is around $177 million. Aave's security module Umbrella, used to absorb default losses, has a WETH reserve of around $50 million with a coverage ratio of less than 30%, with the remaining amount to be borne by aWETH stakers.
This ultimately falls on those who simply wanted to earn some WETH interest.
As of the time of writing, LayerZero is still conducting a joint investigation with the security emergency response organization SEAL Org and plans to release a post-incident analysis report in collaboration with Kelp DAO once all information is obtained. Kelp DAO has stated that they are working on "active remediation."
The $293 million exploit is not in the code. The phrase "audit passed" did not cover the location of that parameter.
You may also like

DWF Deep Report: AI in DeFi Outperforms Humans in Yield Optimization, but Complex Trades Still Lag Behind by 5 Times

The Risk Management Core Team has just been ousted, and Aave is now facing a $200 million default.

a16z on Recruitment: How to Choose Between Crypto-Native and Traditional Talent?

The biggest DeFi heist of 2026, hackers easily took advantage of Aave

Will Robots Replace Humans? He Says No!

Binance Coin's Price Skyrockets 15x to All-Time High, Saved by Three Bull Market Lifelines

The organization has accessed the prediction market, but is stuck at the third stage

Head of crypto VC collective shrinks: a16z crypto fund management scale plummets by 40%, Multicoin cut in half

Arthur Hayes New Post: It's "No Trade" Time Now

Claude Opus 4.7 Review: Is It Worthy of the Title of Strongest Model?

DWF In-Depth Report: AI Outperforms Humans in Yield Farming Optimization in DeFi, But Complex Transactions Still Lag Behind 5x

The financial tricks of the crypto giant Kraken

When proactive market makers start to take initiative

Massive Whale Movement: Unstaking $84.96 Million in HYPE Tokens
Key Takeaways A crypto whale, known as TechnoRevenant, has unstaked approximately $84.96 million in HYPE tokens. The tokens…

ListaDAO Addresses Third-Party Contract Vulnerability Concerns
Key Takeaways GoPlus Security revealed a vulnerability in a contract resembling those of ListaDAO. ListaDAO confirmed that their…

Security Risks of Fake Ledger Nano S+ Devices Emerging Through Chinese E-Commerce
Key Takeaways Counterfeit Ledger Nano S+ devices are being sold on Chinese e-commerce platforms, posing significant risks to…

Wave of Cyber Attacks Hits DeFi Protocols Post-Drift Hack
Key Takeaways A significant $280 million attack on Drift Protocol set off a chain of security breaches across…

Tom Lee Says ‘Mini Crypto Winter’ Is Over, Sees Ether Above $60K
Key Takeaways: Tom Lee predicts Ether’s resurgence, projecting it to surpass $60,000 in the coming years. Bitmine suffered…


